Cybersecurity threats multiply in the midst of Russia-Ukraine conflict
Companies and institutions must prepare themselves for potential threats by taking a complete inventory of their digital defense tools and practices. This is an opportunity to strengthen them in order to limit the impact of an attack in a long-term global cybersecurity approach.
Physical warfare on military operations grounds is now coupled with cyberwarfare, which involves hackers mandated by governments or belonging to independent groups such as Anonymous. The Russian digital offensive has already claimed its first victims, with some ten thousand French and European subscribers to the Viasat satellite network operated by Nordnet no longer having access to the Internet.
In the camp of Russia's opponents, several cyber attacks of the denial of service (DoS) type, claimed by Anonymous, have targeted many official sites in Russia, including the one of the Kremlin, the lower house of the Russian Parliament and the Ministry of Defense. These attacks have also affected telephone operators and the media.
Faced with these threats, national government services are in battle order. In France, the National Agency for Information Systems Security (ANSSI) recommends the implementation of 5 priority preventive measures.
The first one is to reinforce authentication on information systems. The agency strongly advises to implement a strong authentication requiring the use of two different authentication factors.
Either a password, an unlocking trace or a signature. Or, a hardware support (smart card, USB token, magnetic card, RFID) or at least, another code received by another channel (SMS).
On the administrator side, the activation of a reinforced authentication must be done on all accounts: Active Directory, application administration, cloud, etc.
Regular offline backup, a pillar of preventive cybersecurity policies
The second piece of advice from Anssi is based on the supervision of recorded events. In Active Directory environments, abnormal connections on domain controllers should be analyzed. Sensitive points include VPN access, virtual desktops, or hypervisors. Whenever possible, an IS security assessment should be performed with Sysmon, Edr or Xdr tools.
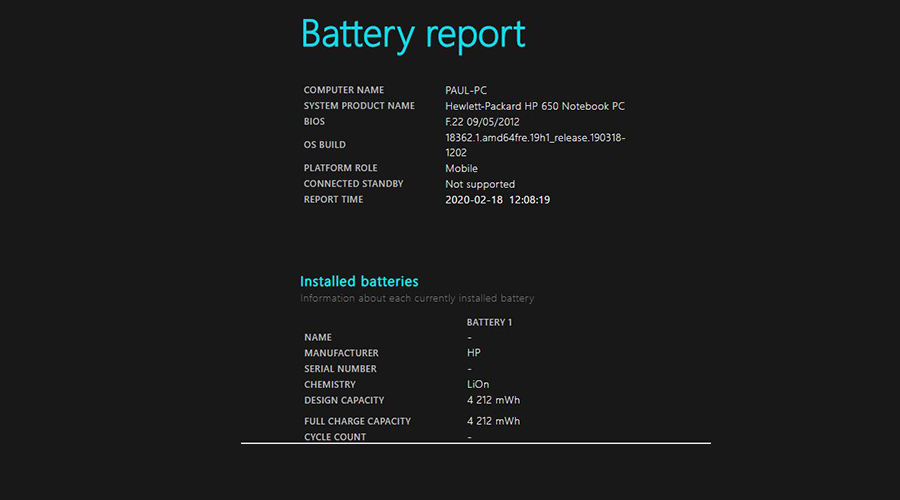
Thirdly, it is necessary to make regular backups of all data, including those on file servers, infrastructure and critical business applications.
For critical data, the disconnection between the active information system and the storage solutions on external hard disks or magnetic tapes is strongly recommended to avoid their encoding. Of course, backups must be updated frequently.
It is also important to have a precise and prioritized inventory of sensitive data for the company by consulting all the business managers. Dependencies on service providers must not be forgotten.
The last piece of advice concerns the presence of a crisis plan that allows for the gradual resumption of activity. During a severe attack, most IS services operate in degraded mode or worse, require the use of paper and pencil. Emergency contact points must be defined, including those of digital service providers.
The IT recovery plan aims, among other things, to provide for the restoration of systems and data. Hence the major interest in having up-to-date backups, which is not always the case in companies and institutions.
Source : itsocial